Innovation Across Emerging Technologies
Welcome to the Wipro Innovation Network – a catalyst for AI-powered co-innovation.
The Wipro Innovation Network is an integral part of Wipro Intelligence™ - our unified suite of AI platforms, solutions, and transformative offerings designed to help our clients scale with confidence, and lead in an AI-powered world.
By bringing together our global ecosystem of labs, partners, start-ups, academia, and deep-tech talent, we accelerate innovation that solves real-world challenges, unlocks bold new possibilities, and drives competitive edge for our clients. This ecosystem harnesses frontier technologies to power transformative solutions and ensure our clients stay ahead in an increasingly complex and fast-evolving landscape.
An integrated innovation ecosystem, powered by Wipro Intelligence™
Experience the Wipro Innovation Network.
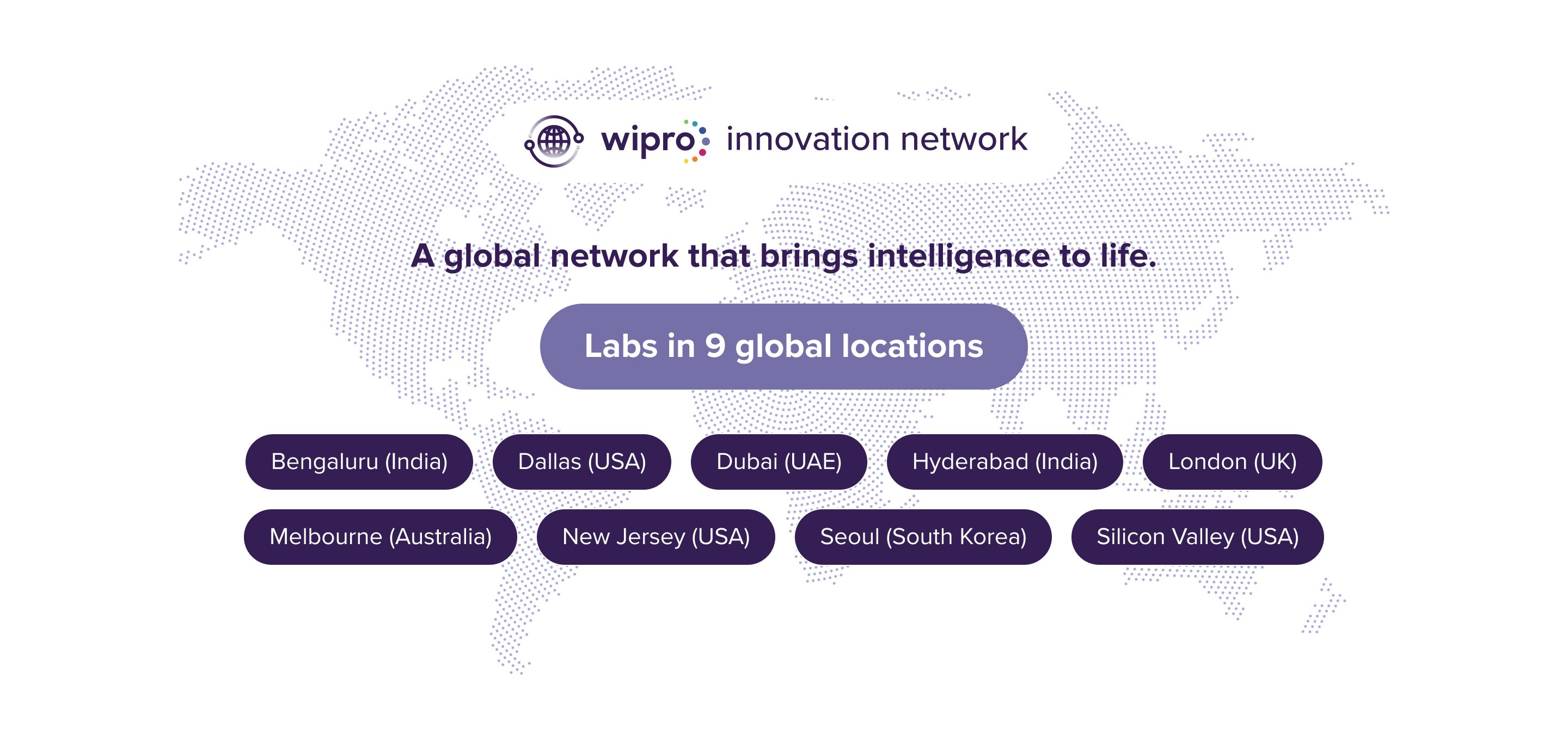
The Wipro Innovation Network is global, interconnected and AI-powered
Wipro’s Tech Trends for 2026
Highlights seven transformative shifts redefining enterprises and human–machine collaboration in an increasingly autonomous, intelligent world.
Customer
Success Stories.
How Wipro uses consulting-led, AI-powered strategies to help customers realize their ambitions.
State of Data4AI Report 2025
Journeys to Help CDAOs Scale Enterprise-Level AI
State of Cybersecurity Report 2025.
AI Strengthens and Disrupts Cyber Resilience.
Innovation Across Emerging Technologies
Thought Leadership