June | 2021
In the post COVID-19 world, businesses are looking for ways to be more agile and reduce latency driven by traditional ways of working. This is not only reflected in their back-office processes but also in their customer facing ones. They are increasingly relying on hyper automation and artificial intelligence (AI) to solve complex business problems. Cybersecurity and risk programs should be part of this AI-led approach. With the need to reduce operating cost across enterprises, AI has become the hallmark for driving the 3Es – Efficiency, Economics and Experience.
Understanding what the AI technologies can do for you, how you can get past the adoption hurdles, and how to achieve non-linear growth in speed, scale and agility are some of the biggest challenges we face when considering the use of AI in cybersecurity and risk. In addition, use of AI solutions should not be interpreted as “replacing a team” but instead, complementing your team to increase productivity. As such, the use of AI should be core to your cybersecurity strategy.
Common AI methods applied across cyber
There are several techniques that are commonly used in AI such as deep learning neural networks, decision trees, Monte Carlo methods, clustering, ranking, linear classifiers (Fisher’s method, Support Vector Machine), Bayesian Statistical Inference, Markov chain, Linguistics, and Bias. These are broadly applied across seven methods, described below and in Figure 1:
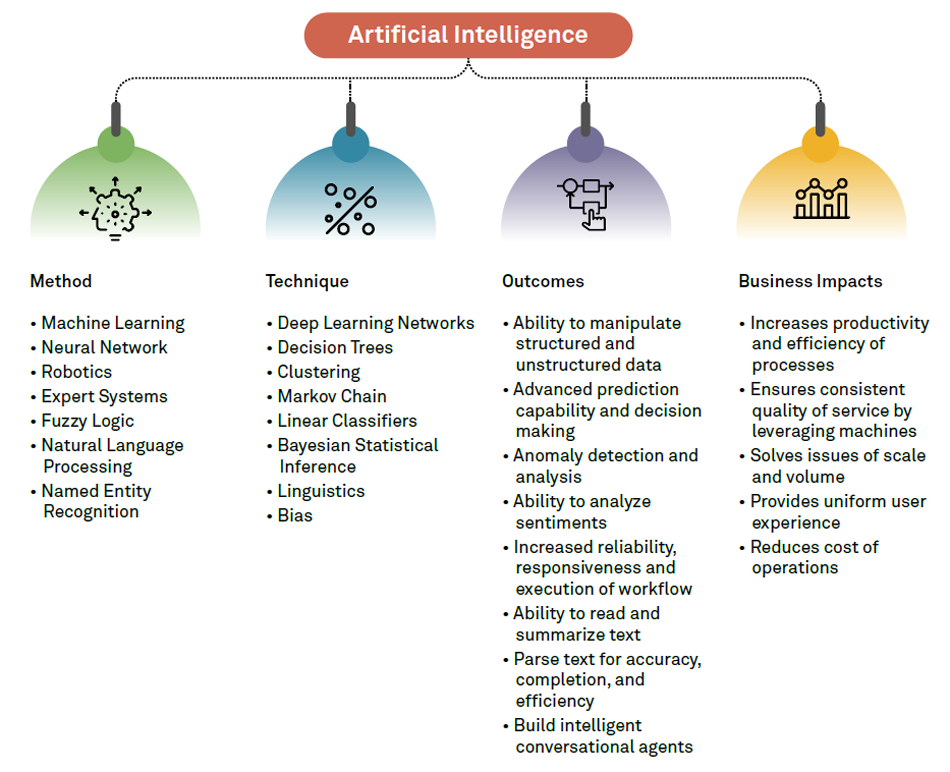
Figure 1: Common AI methods for cyber and their impact
Applicability of AI across cyber
According to Wipro’s State of Cybersecurity Report 2020, 49% of the cybersecurity patent filings were in the AI/ML and data science space. The report also predicted that over a 12-to-16 month period, AI/ML and SOAR (security orchestration, automation and response) will become mainstream to cybersecurity automation.
The application of artificial intelligence should be explored across all facets of cybersecurity from the perspective of process efficiency and business outcomes. This requires reimagining the existing business processes to embrace a robust and effective approach. The matrix in Figure 2 highlights key cyber domains and how they map against AI methods.

How can Wipro help you in your cyber-AI journey?
Wipro’s Cybersecurity and Risk Services partners with the Wipro HOLMES™ team comprising data scientists, stewards, and engineers skilled in AI techniques. Combined with Wipro’s rich technology heritage, we can provide our customers a holistic AI-enabled business transformation service.
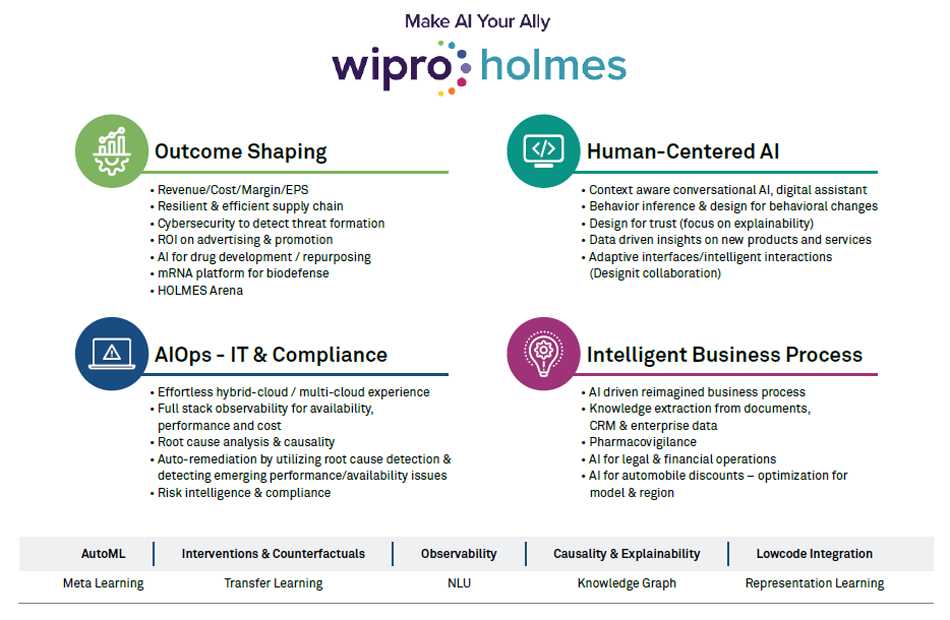
Figure 3: Holistic AI-enabled transformation
Considering the factors that make AI enablement a success, Wipro has created a delivery framework for AI-enabled transformation in cyber:
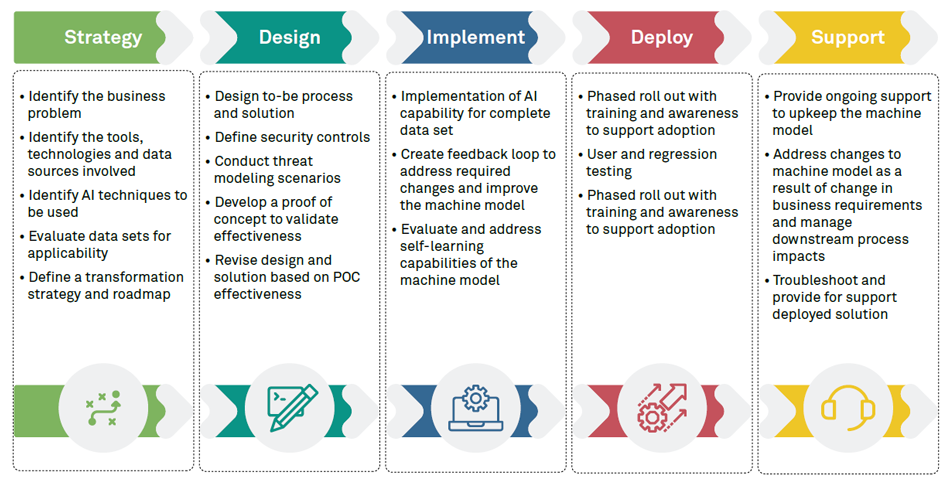
Figure 4: Wipro's delivery framework
Wipro HOLMES™, Wipro's AI and automation platform, is the bridge between foundational AI algorithm builders and applied AI. The HOLMES platform handles all your needs from building, publishing, metering, governance to monetization of heterogenous AI solutions. It can act as a standalone platform to provide solutions you need and act as a complementary platform with AI capabilities. This flexibility provides Wipro the ability to work with its customers and provide the same set of capabilities on the customers’ infrastructure and platforms
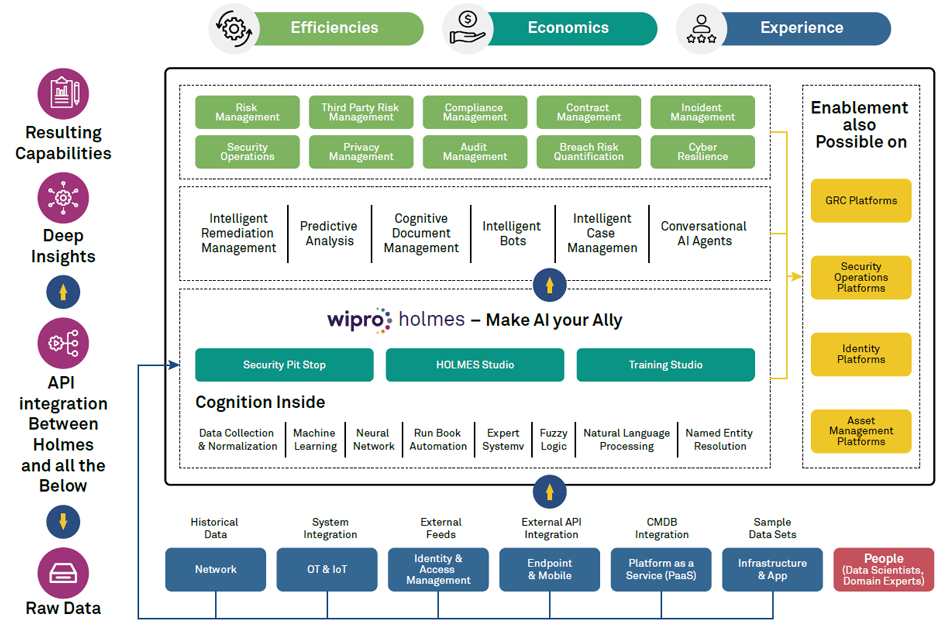
Figure 5: Wipro HOLMES framework
Wipro has been recognized for its holistic AI-enabled transformation solutions:
If you are interested in knowing how Wipro is helping our clients achieve their vision of a transformed AI-powered cybersecurity system, connect with us at cybersecurity.services@wipro.com.
Saugat Sindhu
Global Head - Strategy & Risk Practice - Cybersecurity & Risk Services, Wipro
Saugat is currently leading a team of diverse professionals that provides clients business advisory, management consulting, technology enablement & intelligent automation-based transformation services. He leverages Wipro’s HOLMES ecosystem along with alliance partnerships to bring forth cyber and risk process enhancement strategy and solutions that solve business problems of economics, efficiency, and experience.
Supported by:
Partho Pratim Das
Group Head, HOLMES