September | 2020
Abstract
Wipro and Microsoft recently hosted a joint CISO panel event on the topic of Zero Trust user access for a secure remote working environment. The purpose of this white paper is to discuss the role played by Zero Trust user access in securing the remote working, elaborate some of the key points from the CISO panel discussions and learn how Microsoft security solutions enable organizations to secure their users, devices, network, applications, and data through Zero Trust security approaches.
The trusted perimeter is no longer effective
A rare global crisis like COVID-19 has transformed human life as well as the enterprise operating model. Working remotely on a massive scale is bringing new security challenges to organizations as untrusted networks and unhealthy devices are being leveraged to connect to the enterprise network, systems and services. While leveraging existing remote connectivity solutions and trust-model dependent security solutions to meet the remote working requirements, organizations are witnessing their attack surface grow in today’s increasingly hostile threat landscape. All the CISOs in the panel echoed the same opinion - the need to rethink the fundamentals of perimeter centric and trust-based security and the way it protects enterprise critical applications, data, devices, and users.
Zero Trust – The new security fundamental
Today, organizations require a security model that effectively adapts to the complexity of the current modern workplace environment and safeguard from the evolving threat landscape. It should efficiently support the mobile workforce and protect users, devices, applications, and data wherever they are located.
The Zero Trust security model is not new and it has been in discussions and practice for quite some time. However, it was majorly leveraged in a narrowed scope among risk signal sources such as network, data, applications, users, and devices. They work independently and do not share the threat signals and intelligence with each other, preventing it from being a comprehensive and effective security model. However, they all share the common Zero Trust principles such as:
But with the new normal working atmosphere, we are all in a perimeter-less world and identity is the new perimeter. Hence the Zero Trust should start from the user access, and it is very critical that the enterprise access management solution supports the above three core Zero Trust security principles. Based on a majority view of the CISOs at the panel discussion on the Zero Trust user access, it appears that several organizations are in the process of adopting the Zero Trust security model and would start with identities.
Start your Zero Trust journey with Microsoft Security Stack
Microsoft provides a strong foundational security solution to kick start your zero trust journey. Azure Active Directory Conditional Access helps organization to provide granular access to users and devices to access applications and data securely by leveraging billions of threat signals and providing real-time threat protections.
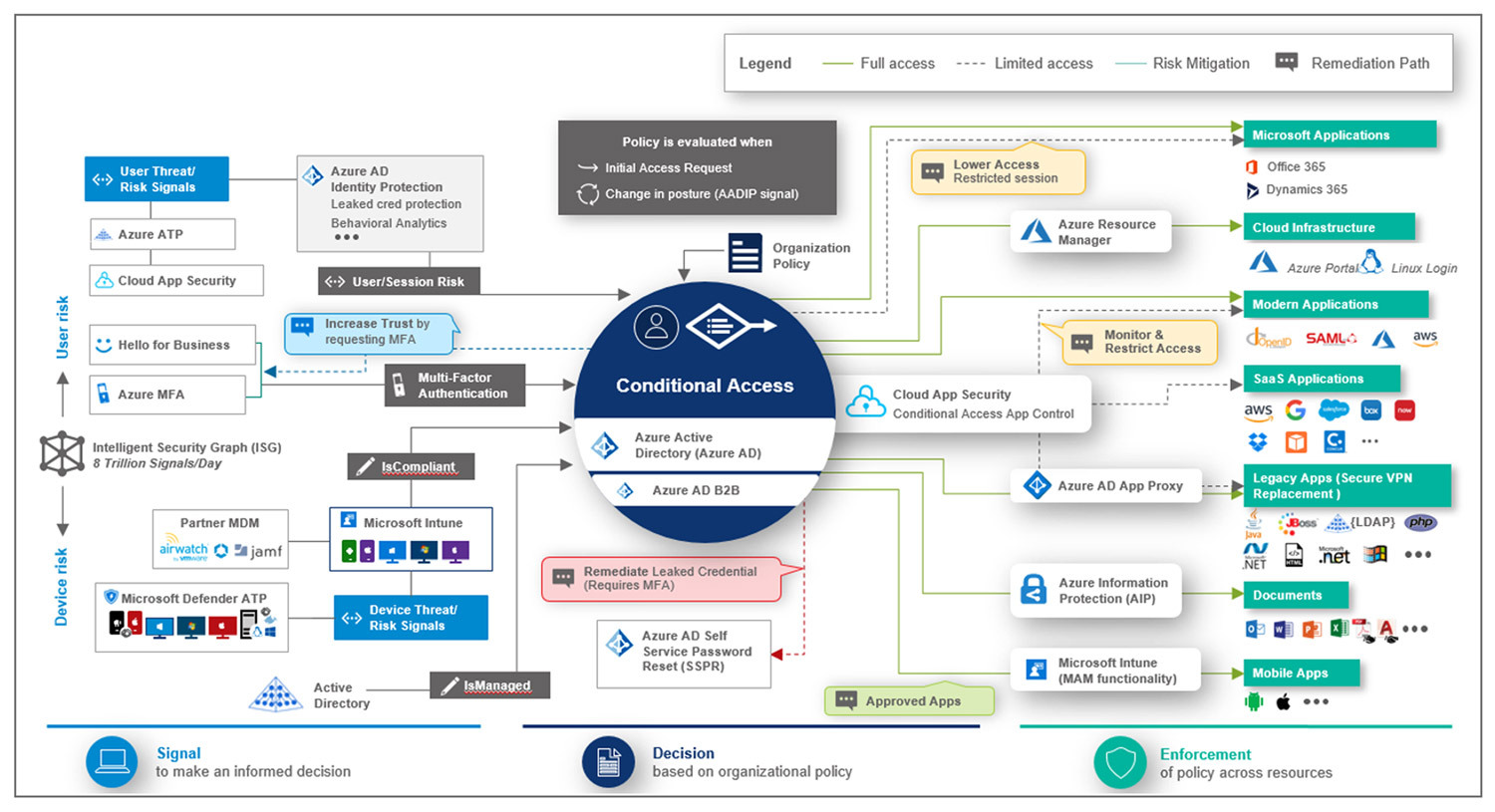
Figure 1: Microsoft working model of Zero Trust User Access reference architecture
Azure AD native integrations with mobile device management systems (Intune), Advanced Threat Protections (ATPs) and Cloud App Security provide a strong Zero Trust orchestration platform to enforce your organizational Zero Trust user access policies. Microsoft Graph APIs allow integrating with third party risk signals and automating real-time risks remediation before the user trust is established to gain access to corporate data.
Microsoft security solutions provide adequate building blocks to drive your Zero Trust user access implementation. Some of the key pillars of the Zero Trust user access include:
Conclusion and Takeaways:
From the collective view points from the panel discussion, it is obvious that most of the organizations are re-prioritizing their security programs to focus on strengthening their remote workplace environment by adopting Zero Trust security principles. Some of the key learnings from this event include:
Prakash Narayanamoorthy
Microsoft Security Practice Partner & Principal Security Architect at Wipro
Prakash Narayanamoorthy is the Microsoft Security Practice Partner & Principal Security Architect at Wipro. He has spent 17+ years in the Identity and Security domain, and helped multiple large global organizations to solve complex IAM challenges. He can be reached out at Prakash.narayanamoorthy@wipro.com